List of Tables
Table 1. Global Identity and Access Management (IAM) Tools Market Size Growth Rate by Type (US$ Million): 2020 VS 2024 VS 2031
Table 2. Key Players of Cloud-Based
Table 3. Key Players of On-Premises
Table 4. Global Identity and Access Management (IAM) Tools Market Size Growth Rate by User (US$ Million): 2020 VS 2024 VS 2031
Table 5. Key Players of Employee IAM
Table 6. Key Players of Consumer IAM
Table 7. Key Players of Partner IAM
Table 8. Key Players of Developer IAM
Table 9. Key Players of IoT IAM
Table 10. Global Identity and Access Management (IAM) Tools Market Size Growth Rate by Industry (US$ Million): 2020 VS 2024 VS 2031
Table 11. Key Players of Healthcare
Table 12. Key Players of Telecommunication
Table 13. Key Players of BFSI
Table 14. Key Players of Media and Entertainment
Table 15. Key Players of Travel aTravel and Hospitalitynd HospitaTravel and Hospitalitylity
Table 16. Global Identity and Access Management (IAM) Tools Market Size Growth by Application (US$ Million): 2020 VS 2024 VS 2031
Table 17. Global Identity and Access Management (IAM) Tools Market Size by Region (US$ Million): 2020 VS 2024 VS 2031
Table 18. Global Identity and Access Management (IAM) Tools Market Size by Region (2020-2025) & (US$ Million)
Table 19. Global Identity and Access Management (IAM) Tools Market Share by Region (2020-2025)
Table 20. Global Identity and Access Management (IAM) Tools Forecasted Market Size by Region (2026-2031) & (US$ Million)
Table 21. Global Identity and Access Management (IAM) Tools Market Share by Region (2026-2031)
Table 22. Identity and Access Management (IAM) Tools Market Trends
Table 23. Identity and Access Management (IAM) Tools Market Drivers
Table 24. Identity and Access Management (IAM) Tools Market Challenges
Table 25. Identity and Access Management (IAM) Tools Market Restraints
Table 26. Global Identity and Access Management (IAM) Tools Revenue by Players (2020-2025) & (US$ Million)
Table 27. Global Identity and Access Management (IAM) Tools Market Share by Players (2020-2025)
Table 28. Global Top Identity and Access Management (IAM) Tools Players by Company Type (Tier 1, Tier 2, and Tier 3) & (based on the Revenue in Identity and Access Management (IAM) Tools as of 2024)
Table 29. Ranking of Global Top Identity and Access Management (IAM) Tools Companies by Revenue (US$ Million) in 2024
Table 30. Global 5 Largest Players Market Share by Identity and Access Management (IAM) Tools Revenue (CR5 and HHI) & (2020-2025)
Table 31. Global Key Players of Identity and Access Management (IAM) Tools, Headquarters and Area Served
Table 32. Global Key Players of Identity and Access Management (IAM) Tools, Product and Application
Table 33. Global Key Players of Identity and Access Management (IAM) Tools, Date of Enter into This Industry
Table 34. Mergers & Acquisitions, Expansion Plans
Table 35. Global Identity and Access Management (IAM) Tools Market Size by Type (2020-2025) & (US$ Million)
Table 36. Global Identity and Access Management (IAM) Tools Revenue Market Share by Type (2020-2025)
Table 37. Global Identity and Access Management (IAM) Tools Forecasted Market Size by Type (2026-2031) & (US$ Million)
Table 38. Global Identity and Access Management (IAM) Tools Revenue Market Share by Type (2026-2031)
Table 39. Global Identity and Access Management (IAM) Tools Market Size by Application (2020-2025) & (US$ Million)
Table 40. Global Identity and Access Management (IAM) Tools Revenue Market Share by Application (2020-2025)
Table 41. Global Identity and Access Management (IAM) Tools Forecasted Market Size by Application (2026-2031) & (US$ Million)
Table 42. Global Identity and Access Management (IAM) Tools Revenue Market Share by Application (2026-2031)
Table 43. North America Identity and Access Management (IAM) Tools Market Size Growth Rate by Country (US$ Million): 2020 VS 2024 VS 2031
Table 44. North America Identity and Access Management (IAM) Tools Market Size by Country (2020-2025) & (US$ Million)
Table 45. North America Identity and Access Management (IAM) Tools Market Size by Country (2026-2031) & (US$ Million)
Table 46. Europe Identity and Access Management (IAM) Tools Market Size Growth Rate by Country (US$ Million): 2020 VS 2024 VS 2031
Table 47. Europe Identity and Access Management (IAM) Tools Market Size by Country (2020-2025) & (US$ Million)
Table 48. Europe Identity and Access Management (IAM) Tools Market Size by Country (2026-2031) & (US$ Million)
Table 49. Asia-Pacific Identity and Access Management (IAM) Tools Market Size Growth Rate by Region (US$ Million): 2020 VS 2024 VS 2031
Table 50. Asia-Pacific Identity and Access Management (IAM) Tools Market Size by Region (2020-2025) & (US$ Million)
Table 51. Asia-Pacific Identity and Access Management (IAM) Tools Market Size by Region (2026-2031) & (US$ Million)
Table 52. Latin America Identity and Access Management (IAM) Tools Market Size Growth Rate by Country (US$ Million): 2020 VS 2024 VS 2031
Table 53. Latin America Identity and Access Management (IAM) Tools Market Size by Country (2020-2025) & (US$ Million)
Table 54. Latin America Identity and Access Management (IAM) Tools Market Size by Country (2026-2031) & (US$ Million)
Table 55. Middle East & Africa Identity and Access Management (IAM) Tools Market Size Growth Rate by Country (US$ Million): 2020 VS 2024 VS 2031
Table 56. Middle East & Africa Identity and Access Management (IAM) Tools Market Size by Country (2020-2025) & (US$ Million)
Table 57. Middle East & Africa Identity and Access Management (IAM) Tools Market Size by Country (2026-2031) & (US$ Million)
Table 58. Microsoft Company Details
Table 59. Microsoft Business Overview
Table 60. Microsoft Identity and Access Management (IAM) Tools Product
Table 61. Microsoft Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 62. Microsoft Recent Development
Table 63. Amazon Web Services Company Details
Table 64. Amazon Web Services Business Overview
Table 65. Amazon Web Services Identity and Access Management (IAM) Tools Product
Table 66. Amazon Web Services Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 67. Amazon Web Services Recent Development
Table 68. HID Global Company Details
Table 69. HID Global Business Overview
Table 70. HID Global Identity and Access Management (IAM) Tools Product
Table 71. HID Global Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 72. HID Global Recent Development
Table 73. IBM Company Details
Table 74. IBM Business Overview
Table 75. IBM Identity and Access Management (IAM) Tools Product
Table 76. IBM Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 77. IBM Recent Development
Table 78. CyberArk Company Details
Table 79. CyberArk Business Overview
Table 80. CyberArk Identity and Access Management (IAM) Tools Product
Table 81. CyberArk Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 82. CyberArk Recent Development
Table 83. OpenText(Micro Focus) Company Details
Table 84. OpenText(Micro Focus) Business Overview
Table 85. OpenText(Micro Focus) Identity and Access Management (IAM) Tools Product
Table 86. OpenText(Micro Focus) Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 87. OpenText(Micro Focus) Recent Development
Table 88. Okta Company Details
Table 89. Okta Business Overview
Table 90. Okta Identity and Access Management (IAM) Tools Product
Table 91. Okta Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 92. Okta Recent Development
Table 93. GoTo Group Company Details
Table 94. GoTo Group Business Overview
Table 95. GoTo Group Identity and Access Management (IAM) Tools Product
Table 96. GoTo Group Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 97. GoTo Group Recent Development
Table 98. Oracle Company Details
Table 99. Oracle Business Overview
Table 100. Oracle Identity and Access Management (IAM) Tools Product
Table 101. Oracle Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 102. Oracle Recent Development
Table 103. Intel Corporation Company Details
Table 104. Intel Corporation Business Overview
Table 105. Intel Corporation Identity and Access Management (IAM) Tools Product
Table 106. Intel Corporation Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 107. Intel Corporation Recent Development
Table 108. Siemens AG Company Details
Table 109. Siemens AG Business Overview
Table 110. Siemens AG Identity and Access Management (IAM) Tools Product
Table 111. Siemens AG Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 112. Siemens AG Recent Development
Table 113. Broadcom Company Details
Table 114. Broadcom Business Overview
Table 115. Broadcom Identity and Access Management (IAM) Tools Product
Table 116. Broadcom Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 117. Broadcom Recent Development
Table 118. Dell Company Details
Table 119. Dell Business Overview
Table 120. Dell Identity and Access Management (IAM) Tools Product
Table 121. Dell Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 122. Dell Recent Development
Table 123. Hitachi Company Details
Table 124. Hitachi Business Overview
Table 125. Hitachi Identity and Access Management (IAM) Tools Product
Table 126. Hitachi Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 127. Hitachi Recent Development
Table 128. Thales Group Company Details
Table 129. Thales Group Business Overview
Table 130. Thales Group Identity and Access Management (IAM) Tools Product
Table 131. Thales Group Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 132. Thales Group Recent Development
Table 133. FusionAuth Company Details
Table 134. FusionAuth Business Overview
Table 135. FusionAuth Identity and Access Management (IAM) Tools Product
Table 136. FusionAuth Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 137. FusionAuth Recent Development
Table 138. ARCON Company Details
Table 139. ARCON Business Overview
Table 140. ARCON Identity and Access Management (IAM) Tools Product
Table 141. ARCON Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 142. ARCON Recent Development
Table 143. SailPoint Company Details
Table 144. SailPoint Business Overview
Table 145. SailPoint Identity and Access Management (IAM) Tools Product
Table 146. SailPoint Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 147. SailPoint Recent Development
Table 148. Google Company Details
Table 149. Google Business Overview
Table 150. Google Identity and Access Management (IAM) Tools Product
Table 151. Google Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 152. Google Recent Development
Table 153. Ping Identity Company Details
Table 154. Ping Identity Business Overview
Table 155. Ping Identity Identity and Access Management (IAM) Tools Product
Table 156. Ping Identity Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 157. Ping Identity Recent Development
Table 158. Delinea Company Details
Table 159. Delinea Business Overview
Table 160. Delinea Identity and Access Management (IAM) Tools Product
Table 161. Delinea Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 162. Delinea Recent Development
Table 163. IDMWORKS Company Details
Table 164. IDMWORKS Business Overview
Table 165. IDMWORKS Identity and Access Management (IAM) Tools Product
Table 166. IDMWORKS Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 167. IDMWORKS Recent Development
Table 168. One Identity Company Details
Table 169. One Identity Business Overview
Table 170. One Identity Identity and Access Management (IAM) Tools Product
Table 171. One Identity Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 172. One Identity Recent Development
Table 173. Asiainfo Security Technologies Co.,Ltd. Company Details
Table 174. Asiainfo Security Technologies Co.,Ltd. Business Overview
Table 175. Asiainfo Security Technologies Co.,Ltd. Identity and Access Management (IAM) Tools Product
Table 176. Asiainfo Security Technologies Co.,Ltd. Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 177. Asiainfo Security Technologies Co.,Ltd. Recent Development
Table 178. SecurLogin Company Details
Table 179. SecurLogin Business Overview
Table 180. SecurLogin Identity and Access Management (IAM) Tools Product
Table 181. SecurLogin Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 182. SecurLogin Recent Development
Table 183. Bamboocloud Co.,Ltd. Company Details
Table 184. Bamboocloud Co.,Ltd. Business Overview
Table 185. Bamboocloud Co.,Ltd. Identity and Access Management (IAM) Tools Product
Table 186. Bamboocloud Co.,Ltd. Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 187. Bamboocloud Co.,Ltd. Recent Development
Table 188. Paraview Software Company Details
Table 189. Paraview Software Business Overview
Table 190. Paraview Software Identity and Access Management (IAM) Tools Product
Table 191. Paraview Software Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 192. Paraview Software Recent Development
Table 193. Trusfort Company Details
Table 194. Trusfort Business Overview
Table 195. Trusfort Identity and Access Management (IAM) Tools Product
Table 196. Trusfort Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 197. Trusfort Recent Development
Table 198. Alibaba Cloud Company Details
Table 199. Alibaba Cloud Business Overview
Table 200. Alibaba Cloud Identity and Access Management (IAM) Tools Product
Table 201. Alibaba Cloud Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 202. Alibaba Cloud Recent Development
Table 203. Tencent Company Details
Table 204. Tencent Business Overview
Table 205. Tencent Identity and Access Management (IAM) Tools Product
Table 206. Tencent Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 207. Tencent Recent Development
Table 208. Neusoft Company Details
Table 209. Neusoft Business Overview
Table 210. Neusoft Identity and Access Management (IAM) Tools Product
Table 211. Neusoft Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 212. Neusoft Recent Development
Table 213. Baidu Company Details
Table 214. Baidu Business Overview
Table 215. Baidu Identity and Access Management (IAM) Tools Product
Table 216. Baidu Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 217. Baidu Recent Development
Table 218. Meicloud Company Details
Table 219. Meicloud Business Overview
Table 220. Meicloud Identity and Access Management (IAM) Tools Product
Table 221. Meicloud Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 222. Meicloud Recent Development
Table 223. QI-ANXIN Technolody Group Inc. Company Details
Table 224. QI-ANXIN Technolody Group Inc. Business Overview
Table 225. QI-ANXIN Technolody Group Inc. Identity and Access Management (IAM) Tools Product
Table 226. QI-ANXIN Technolody Group Inc. Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 227. QI-ANXIN Technolody Group Inc. Recent Development
Table 228. Huawei Cloud Company Details
Table 229. Huawei Cloud Business Overview
Table 230. Huawei Cloud Identity and Access Management (IAM) Tools Product
Table 231. Huawei Cloud Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 232. Huawei Cloud Recent Development
Table 233. DKEY Token Company Details
Table 234. DKEY Token Business Overview
Table 235. DKEY Token Identity and Access Management (IAM) Tools Product
Table 236. DKEY Token Revenue in Identity and Access Management (IAM) Tools Business (2020-2025) & (US$ Million)
Table 237. DKEY Token Recent Development
Table 238. Research Programs/Design for This Report
Table 239. Key Data Information from Secondary Sources
Table 240. Key Data Information from Primary Sources
Table 241. Authors List of This Report
List of Figures
Figure 1. Identity and Access Management (IAM) Tools Picture
Figure 2. Global Identity and Access Management (IAM) Tools Market Size Comparison by Type (2020-2031) & (US$ Million)
Figure 3. Global Identity and Access Management (IAM) Tools Market Share by Type: 2024 VS 2031
Figure 4. Cloud-Based Features
Figure 5. On-Premises Features
Figure 6. Global Identity and Access Management (IAM) Tools Market Size Comparison by User (2020-2031) & (US$ Million)
Figure 7. Employee IAM Features
Figure 8. Consumer IAM Features
Figure 9. Partner IAM Features
Figure 10. Developer IAM Features
Figure 11. IoT IAM Features
Figure 12. Global Identity and Access Management (IAM) Tools Market Size Comparison by Industry (2020-2031) & (US$ Million)
Figure 13. Healthcare Features
Figure 14. Telecommunication Features
Figure 15. BFSI Features
Figure 16. Media and Entertainment Features
Figure 17. Travel aTravel and Hospitalitynd HospitaTravel and Hospitalitylity Features
Figure 18. Global Identity and Access Management (IAM) Tools Market Size by Application (2020-2031) & (US$ Million)
Figure 19. Global Identity and Access Management (IAM) Tools Market Share by Application: 2024 VS 2031
Figure 20. Large Enterprises Case Studies
Figure 21. SMEs Case Studies
Figure 22. Identity and Access Management (IAM) Tools Report Years Considered
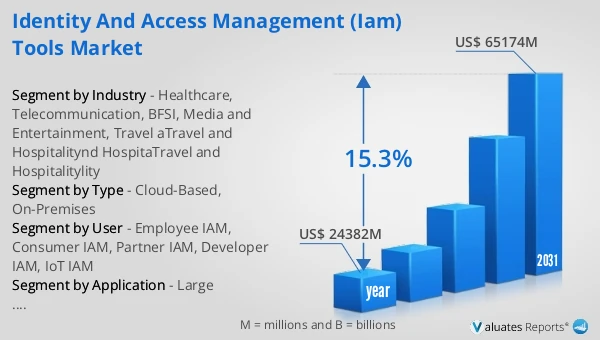
Figure 23. Global Identity and Access Management (IAM) Tools Market Size (US$ Million), Year-over-Year: 2020-2031
Figure 24. Global Identity and Access Management (IAM) Tools Market Size, (US$ Million), 2020 VS 2024 VS 2031
Figure 25. Global Identity and Access Management (IAM) Tools Market Share by Region: 2024 VS 2031
Figure 26. Global Identity and Access Management (IAM) Tools Market Share by Players in 2024
Figure 27. Global Identity and Access Management (IAM) Tools Market Share by Company Type (Tier 1, Tier 2, and Tier 3)
Figure 28. The Top 10 and 5 Players Market Share by Identity and Access Management (IAM) Tools Revenue in 2024
Figure 29. North America Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 30. North America Identity and Access Management (IAM) Tools Market Share by Country (2020-2031)
Figure 31. United States Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 32. Canada Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 33. Europe Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 34. Europe Identity and Access Management (IAM) Tools Market Share by Country (2020-2031)
Figure 35. Germany Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 36. France Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 37. U.K. Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 38. Italy Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 39. Russia Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 40. Ireland Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 41. Asia-Pacific Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 42. Asia-Pacific Identity and Access Management (IAM) Tools Market Share by Region (2020-2031)
Figure 43. China Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 44. Japan Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 45. South Korea Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 46. Southeast Asia Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 47. India Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 48. Australia & New Zealand Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 49. Latin America Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 50. Latin America Identity and Access Management (IAM) Tools Market Share by Country (2020-2031)
Figure 51. Mexico Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 52. Brazil Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 53. Middle East & Africa Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 54. Middle East & Africa Identity and Access Management (IAM) Tools Market Share by Country (2020-2031)
Figure 55. Israel Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 56. Saudi Arabia Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 57. UAE Identity and Access Management (IAM) Tools Market Size YoY Growth (2020-2031) & (US$ Million)
Figure 58. Microsoft Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 59. Amazon Web Services Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 60. HID Global Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 61. IBM Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 62. CyberArk Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 63. OpenText(Micro Focus) Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 64. Okta Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 65. GoTo Group Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 66. Oracle Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 67. Intel Corporation Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 68. Siemens AG Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 69. Broadcom Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 70. Dell Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 71. Hitachi Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 72. Thales Group Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 73. FusionAuth Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 74. ARCON Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 75. SailPoint Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 76. Google Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 77. Ping Identity Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 78. Delinea Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 79. IDMWORKS Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 80. One Identity Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 81. Asiainfo Security Technologies Co.,Ltd. Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 82. SecurLogin Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 83. Bamboocloud Co.,Ltd. Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 84. Paraview Software Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 85. Trusfort Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 86. Alibaba Cloud Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 87. Tencent Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 88. Neusoft Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 89. Baidu Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 90. Meicloud Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 91. QI-ANXIN Technolody Group Inc. Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 92. Huawei Cloud Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 93. DKEY Token Revenue Growth Rate in Identity and Access Management (IAM) Tools Business (2020-2025)
Figure 94. Bottom-up and Top-down Approaches for This Report
Figure 95. Data Triangulation
Figure 96. Key Executives Interviewed